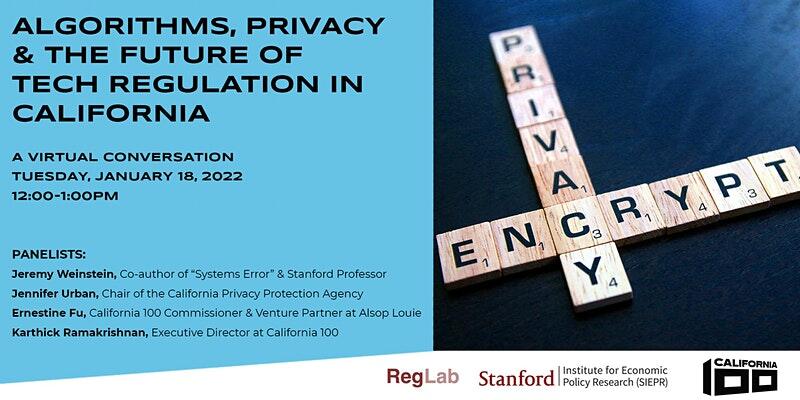
Algorithms, Privacy & the Future of Tech Regulation in California
California-grown technology has led the nation and world in multiple ways—from democratizing the ways we live, work and play, to posing enormous ethical and social challenges that have fueled demands for government regulation.
When, and how, should state governments regulate the harms caused by new technologies? And what are the conditions under which industry self-regulation more appropriate? How do we balance the need to encourage innovation while also protecting communities from harm?
Join experts in academia, industry, and government in a deeper conversation about algorithms, privacy, and the future of tech regulation in California.
Featuring Jeremy Weinstein (Stanford professor and co-author of the recent book System Error), Jennifer Urban (Board Chair of the California Privacy Protection Agency), Ernestine Fu (California 100 Commissioner and Venture Partner, Alsop Louie), and Karthick Ramakrishnan (Executive Director, California 100) as the moderator, this discussion will cover present-day challenges and remedies on data privacy and lack of consumer power, as well as larger questions about when and how to step into future regulation conversations involving new technologies.


 Jenny Jun is a PhD Candidate in the Department of Political Science at Columbia University and Nonresident Fellow at the Atlantic Council’s Cyber Statecraft Initiative. Her current research explores the dynamics of coercion in cyberspace. Her broader interests include cyber conflict, North Korea, and security issues in East Asia. Jenny is a co-author of the 2015 Center for Strategic and International Studies (CSIS) report North Korea’s Cyber Operations: Strategy and Responses, published by Rowman & Littlefield. She has presented her work on North Korea’s cyber operations at various panels and has provided multiple government briefings and media interviews on the topic. She received her MA and BS each from the Security Studies Program (SSP) and the School of Foreign Service (SFS) at Georgetown University.
Jenny Jun is a PhD Candidate in the Department of Political Science at Columbia University and Nonresident Fellow at the Atlantic Council’s Cyber Statecraft Initiative. Her current research explores the dynamics of coercion in cyberspace. Her broader interests include cyber conflict, North Korea, and security issues in East Asia. Jenny is a co-author of the 2015 Center for Strategic and International Studies (CSIS) report North Korea’s Cyber Operations: Strategy and Responses, published by Rowman & Littlefield. She has presented her work on North Korea’s cyber operations at various panels and has provided multiple government briefings and media interviews on the topic. She received her MA and BS each from the Security Studies Program (SSP) and the School of Foreign Service (SFS) at Georgetown University.





