NSA phone records yield private medical, financial and legal data
The National Security Agency's mass surveillance of telephone metadata could yield detailed information about the private lives of individuals far beyond what the federal government claims, according to new Stanford research.
Stanford computer science student and CISAC cybersecurity fellow Jonathan Mayer and a fellow CS student, Patrick Mutchler, were able to acquire detailed information about people's lives just from telephone metadata: the phone number of the caller and recipient, the particular serial number of the phones involved, the time and duration of calls and possibly the location of each person when the call occurred.
The researchers did not do any illegal snooping – they worked with the phone records of 546 volunteers, matching phone numbers against the public Yelp and Google Places directories to see who was being called.
From the phone numbers, it was possible to determine that 57 percent of the volunteers made at least one medical call. Forty percent made a call related to financial services.
The volunteers called 33,688 unique numbers; 6,107 of those numbers, or 18 percent, were isolated to a particular identity.
Privacy issues
The metadata issue has taken on urgency in the wake of last summer's revelations about surveillance of American citizens by the NSA. Privacy experts have questioned the federal government's assertions on the subject.
President Obama has said, "They are not looking at people's names, and they're not looking at content."
Federal judges have split on the legality of the NSA's telephone metadata program.
Jonathan Mayer talks to Hari Sreenivasan on PBS Newshour in this video:
Computer scientists such as Mayer say metadata are extremely sensitive and revealing.
They contend their research shows that metadata from phone calls can yield a wealth of detail about family, political, professional, religious and sexual associations.
"It would be no technical challenge to scale these identifications to a larger population," said Mayer.
At the outset, Mayer said, they asked, "Is it easy to draw sensitive inferences from phone metadata? How often do people conduct sensitive matters by phone? We turned to our crowdsourced MetaPhone dataset for empirical answers."
They crowdsourced the data using an Android application and conducted an analysis of individual calls made by the volunteers to sensitive numbers, connecting the patterns of calls to emphasize the detail available in telephone metadata, Mayer said.
"A pattern of calls will, of course, reveal more than individual call records," he said. "In our analysis, we identified a number of patterns that were highly indicative of sensitive activities or traits."
For example, one participant called several local neurology groups, a specialty pharmacy, a rare-condition management service, and a pharmaceutical hotline used for multiple sclerosis.
Another contacted a home improvement store, locksmiths, a hydroponics dealer and a head shop.
'Unambiguously sensitive'
The researchers initially shared the same hypothesis as their computer science colleagues, Mayer said. They did not anticipate finding much evidence one way or the other.
"We were wrong. Phone metadata is unambiguously sensitive, even over a small sample and short time window. We were able to infer medical conditions, firearm ownership and more, using solely phone metadata," he said.
All three branches of the federal government are now considering curbs on access to telephone metadata, Mayer noted. Consumer privacy concerns are also salient as the Federal Communications Commission assesses telecom data sharing practices, he added.

MetaPhone: The NSA Three-Hop
First paragraph of the article:
MetaPhone is a crowdsourced study of phone metadata. If you own an Android smartphone, please consider participating. In an earlier post, we reported how automated analysis of call and text activity can detect private relationships.
Does the National Security Agency have court authority to pour over your phone records? Quite possibly.
According to declassified documents, the NSA operates under a rote legal procedure for querying domestic phone metadata. The agency begins by identifying a “seed” number, with reasonable and articulable suspicion of terrorist activity. Next, the NSA has discretion to follow up to three degrees of calling separation (“hops”). The NSA is authorized to retrieve a complete set of phone records at each hop, and just one call in the past five years appears sufficient to make a hop.
Vinton Cerf to talk about safety and security in a wired-up world
Vinton Cerf, who helped develop the Internet while at Stanford in the 1970s, will deliver the 2014 Drell Lecture at Stanford on Jan. 22. Now the vice president and chief Internet evangelist at Google, Cerf will talk about safety and security in a transnational environment.
Vinton Cerf, a pioneering computer scientist who helped launch the Internet, will talk at Stanford University on Jan. 22 about security in our highly wired, globalized world.
Cerf's talk, "Safety and Security in a Transnational World," is the 2014 installment of the Drell Lecture, which is sponsored by Stanford's Center for International Security and Cooperation at the Freeman Spogli Institute for International Studies. The lecture is named for CISAC's co-founder, Sidney Drell.
The event will take place from 4:30 p.m. to 6 p.m. in the Oak Lounge on the second floor of Tressider Memorial Union. The event is free and open to the media and public; no RSVP is required.
Cerf, who earned a bachelor's degree in mathematics at Stanford University, worked in the Silicon Valley computer industry before serving as an assistant professor at Stanford from 1972 to1976. During that time, he helped co-design the fundamental architecture underlying the Internet. In 1997, President Bill Clinton presented the U.S. National Medal of Technology to Cerf and his colleague, Robert E. Kahn, for founding and developing the Internet. Since 2005, Cerf has worked as the vice president and chief Internet evangelist for Google.
Cerf's lecture will include moderated questions and will be live-streamed online at www.ustream.tv/channel/stanford-cisac. CISAC will also be live-tweeting during the event and you can follow the conversation at #VintCerfFSI.
Clifton B. Parker is a writer for the Stanford News Service.
NSA's Creative Interpretations of Law Subvert Congress and the Rule of Law
CISAC Affiliate and Forbes Contributor Jennifer Granick explains how NSA domestic surveillance activities might continue, even in the face of legal decisions to rein in the agency's activities.
Even after the District Court for the District of Columbia ruled that the bulk collection of phone metadata violated the Fourth Amendment, Deputy Attorney General James Cole signaled that the NSA's behavior change will depend on how the court interprets provisions in the legislation.
Granick argues that Cole's comments reflect the Executive Branch's increasing dismissal of Congressional oversight. This trend threatens more than just individual privacy.
Honors Student Mailyn Fidler awarded Marshall Scholarship
CISAC Honors Student Mailyn Fidler has been awarded a Marshall Scholarship to continue her studies in international technology policy. She investigates security implications of the global trade in "zero-day" software exploits. Fidler has also worked as a consultant for Google Glass, autonomous vehicles and Internet access through atmospheric balloons, and was the co-founder and co-editor-in-chief of the Stanford Journal of Public Health.
Marshall Scholarships are named for former U.S. Secretary of State and U.S. Army General George Marshall, and are given to intellectually distinguished Americans to study in Britain.

How the Internet Became Untrustworthy
About the Topic: The Internet in 2014 is a marvelous communication utility. It provides cheap and fast transfer of information to and from most places on or near the surface of Earth. It also regularly betrays that information to curious onlookers, commercial entities, criminals, and governments. We will explore the origins of the Internet, the workings of its core protocols, exploits which take advantage of those protocols, and feeble attempts to make those protocols secure. In sum, we will describe the devolution of the Internet from a peaceful commons to the jungle it is today.
About the Speaker: Tom Berson is a CISAC affiliate and the founder of Anagram Laboratories. He is a cryptographer who views cryptography broadly as the science and ethics of trust and betrayal. He has spent his career working both the defensive and the offensive sides of the information security battle and is attracted most strongly to security issues raised at the confluence of technology, business, and world events.
Tom is a student of Sun Tzu’s Art of War and its applicability to modern information conflict. He was the first person to be named a Fellow of the International Association for Cryptologic Research. His citation reads, “For visionary and essential service and for numerous valuable contributions to the technical, social, and commercial development of cryptology and security.” He was an editor of the Journal of Cryptology for fourteen years. He is a Past-Chair of the IEEE Technical Committee on Security and Privacy.
Tom earned a B.S. in physics from the State University of New York in 1967 and a Ph.D. in computer science from the University of London in 1977. He was a Visiting Fellow in Mathematics in the University of Cambridge, and is a life member of Clare Hall, Cambridge. Tom has been a member of several National Research Council committees: including the Committee on Computer Security in the Department of Energy, the Committee to Review DoD C4I Plans and Programs, and the Committee on Offensive Information Warfare.
CISAC Conference Room
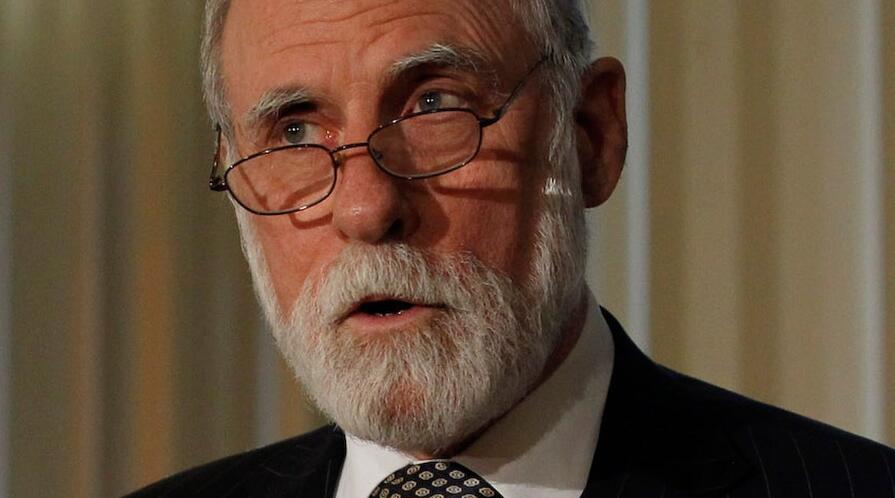
Former FBI director targets cybercrimes
Calling cybercrimes “the threat of the future,” former FBI Director Robert Mueller said federal investigators and businesses need to share information collected online in order to find and thwart hackers trying to disrupt Web-based networks.
“The intelligence that can be and is being collected by the private sector has to be made available in some way, shape or form to the federal government,” Mueller said. “And that which we pick up has to be made available to the private sector. If we do not get that kind of collaboration, we will replicate what we had before 9/11 when we had stovepipes and inadequate ways of sharing information.”
Mueller – who took over the FBI a week before the Sept. 11 terrorist attacks and left the job two months ago – made his comments Friday while delivering the Payne lecture at Stanford.
“Terrorism remains today our primary threat,” Mueller said. “But tomorrow, it will probably be cyber and its various iterations.”
He said cybercrimes present a new challenge to law enforcement agencies because perpetrators are often anonymous and their motives are not always clear.
A hacker could be associated with a terrorist organization, an activist group or “an 18-year-old in his garage here in Silicon Valley who has the talent and capability and wants to make a point.”
And if the bad guy can’t be easily fingered, it’s difficult to know who should investigate the crime – the FBI, CIA, NSA or another agency. In order to pool federal resources, Mueller said a task force composed of 18 agencies works to examine cyber threats.
But their efforts to safeguard online financial, government, corporate and educational systems will go only so far without the expertise, knowledge and information gathered by Internet service providers.
“It is going to be the relationships with the private sector that are going to be absolutely critical to any success we can have in addressing cyber attacks,” he said.
Mueller’s lecture capped his weeklong visit at Stanford. He was invited by the Freeman Spogli Institute for International Studies and Stanford Law School to spend the academic year as a consulting professor and as the Payne Distinguished Lecturer.
The Payne Lectureship is named for Frank E. Payne and Arthur W. Payne, brothers who gained an appreciation for global problems through their international business operations. The position is given to someone with an international reputation as a leader, with an emphasis on visionary thinking; a broad, practical grasp of a given field; and the capacity to clearly articulate an important perspective on the global community and its challenges.
FSI Director Mariano-Florentino Cuéllar called Mueller a “perfect fit for Stanford.”
“His career embodies what I take to be the ethos of this university –practical yet principled; sensitive to complexity but also to the value of clarity and focus,” Cuéllar said.
Mueller will make several visits to Stanford during the year, spending his time working with FSI and law school scholars to develop research agendas on emerging issues in international security. He will hold graduate seminars and deliver a major lecture at the law school and work with students and fellows at the Haas Center, the law school and the Graduate School of Business. He will also mentor honors students at FSI’s Center for International Security and Cooperation and Center on Democracy, Development, and the Rule of Law.
As the FBI’s longest-serving director after J. Edgar Hoover, Mueller presided over some of the most drastic changes in the agency’s history.
The Sept. 11 attacks forced the FBI to change its priorities, placing the hunt for global terrorists at the top if its list. The counterterrorism and counterintelligence missions meant hiring more analysts and replacing the FBI’s more traditional targeting of mobsters, murderers and white-collar criminals.
Recalling his first briefing to George W. Bush after the terrorist attacks, Mueller said he began by telling the president what his agents were doing to investigate. He had been on the job for about a week, and started giving a rundown of command centers that were set up, evidence that was being collected and interviews being conducted.
“I’m about two or three minutes into it and President Bush stops me and says, `Bob, that’s all well and good,’” Mueller said. “That’s what the FBI has been doing for the hundred years of its existence. My question to you is: What is FBI doing to prevent the next terrorist attack?”
The question stumped the new director.
“I had not prepared for that question,” he said.
And it’s a question he answered continuously during the Bush and Obama administrations, and one that led to his reorganization of the FBI.
“Over those 12 years, the question has not changed,” Mueller said. “The question from both of the presidents to the FBI, to the CIA, to the community when it comes to counterterrorism is: What have you done to prevent the next terrorist attack?”
Compromised by Design? Securing the Defense Electronics Supply Chain
CISAC affiliate John Villasenor argues in this Brookings paper that the country's defense electronics supply chain is almost completely unprotected against a threat that may turn out to be more significant in the long term: Chips could be intentionally compromised during the design process, before they are even manufactured.
The paper aims to help frame the discussion regarding how best to respond to this important and underappreciated aspect of cybsercurity.
